“The culture and leadership here is outstanding. Being surrounded by smart people working well together because we care about our customers and each other.”
James, Software Engineer
Protect your entrance. Protect your people with Visitor Aware.
At Singlewire Software, we know what we do matters. Our customers tell us every day the difference our solutions make in their lives as they work to keep their people safe. That knowledge creates a passionate team inspired by their positive influence on other people’s lives. It makes serious work a fun and engaging challenge and lets our employees know that people are central to everything we do.

Singlewire Software has been named a 2023 Top Workplace in Madison for the third consecutive year by the Wisconsin State Journal in the mid-size company category. Read More
Flexible Work/Life Balance
There’s a reason our recent employee survey had “flexible” as the top word to describe the culture here. It’s because “work-life balance” isn’t just a phrase we throw around, it’s something we truly believe helps in our success, and why we:
Integrity Built on Transparency
Doing a job well means knowing precisely what’s expected. That’s why we encourage cross-departmental collaboration so people understand how their work impacts the company at large, and why we:
Career Development
At Singlewire, we pride ourselves on our high rate of employee retention. Part of that has to do with delivering products that make a difference in people’s lives, but the other part is investing in the people by:
Social Events
Our team members are more than just their job titles. That’s why we regularly host in- and out-of-office events to relax, get to know one another better, and maybe even spark some fresh ideas. As part of the team you’ll enjoy:
Community Involvement
Our roots are in Madison, and we’re committed to giving back to a community that has given so much to us. Some of the ways the Singlewire team helps include:
IDEA Team
Diversity, equity, and inclusivity drive innovation and are essential for Singlewire’s continued success. This is the founding philosophy behind our Inclusion, Diversity, Equity and Action (IDEA) Team, which helps:
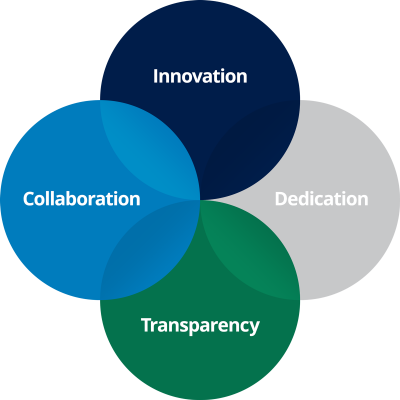
Four core tenets help foster a positive, people-centric culture at Singlewire, and it’s no coincidence that we believe these same tenets are the secret to our customers creating effective strategies that help keep their people safe.
Singlewire Software LLC is an equal opportunity employer. All qualified applicants will receive consideration for employment without regard to race, religion, color, national origin, sex, gender identity, sexual orientation, age, status as a protected veteran, among other things, or status as a qualified individual with disability.
Equal Employment Opportunity Policy | Affirmative Action Policy
Come join our growing team! We offer competitive compensation and provide you, and your dependents, access to a quality employee benefits program to support your long-term health and wellness, including:
Want to know what makes Singlewire one of the best places to work in Madison? Hear it directly from our team members.

“The culture and leadership here is outstanding. Being surrounded by smart people working well together because we care about our customers and each other.”
James, Software Engineer

“There’s a lot of good people in the office who care about their work and care about each other. They’re all wicked smart too. It’s the place to be.”
Travis, Video Production Specialist

“I love the size of Singlewire – we’re big enough to get a lot done, but small enough that everyone’s on a first-name basis. It’s easy to walk over to someone’s desk to get a question answered or a problem solved.”
Daniel, QA Manager

“By far the best thing about Singlewire is the flexibility. Sick? Work from home. Have a dog? Bring them to work. Enjoy talking to your colleagues? Cool, you have awesome colleagues to chat with. Work-life balance? We 100 percent have that here.”
Stephanie, Account Manager